Microsoft recently announced a new existing feature in Microsoft Endpoint Manager with the name: “filters”. With the new feature, it is easier to create a specific deployment and exclude specific device groups. For example excluding virtual desktop machines from the Windows 10 deployment. The feature adds greater flexibility for assigning apps and policies to groups of users or devices.
Important: At the moment of writing filters are still in preview.
With the new filters feature in Microsoft Endpoint Manager it is possible to use filters to target apps, policies, and other workload types to specific devices. Currently, the new feature is in public preview with the may release of Microsoft Intune.
For example, the following scenarios are possible. More specific cases later in the blog with some detailed screenshots.
- A Windows 10 device restriction policy to just the corporate devices of users in the Marketing department while excluding personal devices
- An iOS app to only the iPad devices for users in the Finance group
- An Android compliance policy for mobile phones to all users in the company but exclude Android-based meeting room devices that don’t support the settings in that mobile phone policy
What is supported?
Filters support some of the different workloads available in Microsoft Intune. Important: not all workloads are supported. On the Microsoft docs page the complete list of supported app types, compliance policies, and device configuration profiles. Read the Microsoft docs information page.
Currently, the following features don’t support the new feature:
- Configuration Profile Settings catalog
- App configuration policies for Android and iOS/iPadOS
- App protection policies for Android, iOS/iPadOS, and Windows 10
- End-user experiences customization policies
- Enrollment restrictions
- iOS/iPadOS app provisioning profiles
- Partner device management
- Policies for Office apps
- Policy sets
- PowerShell scripts for Windows 10
- S mode supplemental policies for Windows 10
- Shell scripts for macOS
- Terms and conditions
- Update policies for iOS/iPadOS
- Windows 10 feature updates
- Windows 10 update rings
Filter architecture
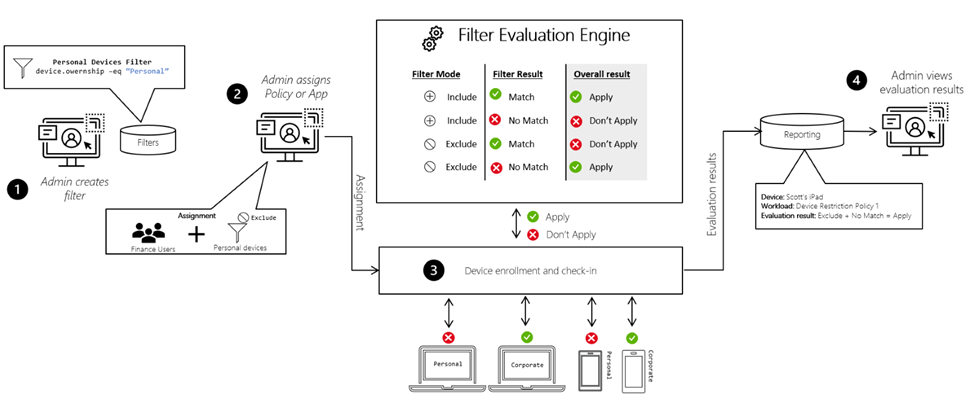
Before a policy is applied to a device, filters dynamically evaluate applicability. Below the architecture view.
Enable the filters feature
Filters are reusable objects, as filters are not related to a specific assignment. That means that filters can be created as separate configurations and works with the Azure AD group assignment or the All users/ All devices property.
The first task is to create a new set of filters with the supported properties and expressions.
To use filters, you must enable it in the tenant.
- Open Endpoint Manager admin center
- Go to: Tenant administration -> Filters (preview) -> Try out the filters (preview) feature
- Set the checkbox Filters preview to on

Once the feature is available, you can see the Create option at the top on the Filters (preview) page.
Create a Filter
- Select Tenant administration > Filters (preview) > Create.
- In Basics, enter the required properties and Click Next.
- Filter name: Enter the name for the filter.
- Description: Enter a description for the filter. This setting is optional
- Platform: Select your platform from available options:
- iOS/iPadOS
- Windows 10
- Android device administrator
- macOS
- Android Enterprise

Now create the rule in Rules. Creating rules is possible with two methods. The rule builder or with the rule syntax. With the Rule syntax builder it is possible to build your own rules in the rule syntax editor.
Based on the selected platform the properties are available. For Windows 10 the selection contains the following properties:
- deviceName
- manufacturer
- model
- deviceCategory
- osVersion
- deviceOwnership
- enrollmentProfilename
- operatingSystemSKU
More information about the Device properties, operators and supported properties for each platform: Microsoft Docs
For example; the following situation. All Windows 10 20H2 devices with the OSversion 10.0.19042 and filled in property device ownership Corporate.
(device.osVersion -eq “10.0.19042”) and (device.deviceOwnership -eq “Corporate”)

In Review + create, review your settings. When you select Create, your changes are saved. The filter is created, and ready to be used for the assignment. After creation the filter is available in the filters list with the added name.

After a filter is created, it can be changed or updated. For changing the existing filter. Open the Filters preview blade in the Tenant administration or go to Devices > Filters (preview) or Apps > Filters (preview).
More examples:
Windows 10 personal devices:
Rule: (device.deviceOwnership -eq “Personal”)
Devices with device model: Surface Book 3, Surface Book 2
Rule: (device.model -in [“Surface Book 3”, “Surface Book 2”])
Autopilot profile filtering: ( profile name based)
(device.enrollmentProfileName -startsWith “AutoPilot Profile”)
All Operating System SKU Enterprise
(device.operatingSystemSKU -in [“Enterprise”, “EnterpriseS”, “EnterpriseN”, “EnterpriseEval”])
Note: The properties, operations, and values are case insensitive. Parentheses and nested parentheses are supported.
Usage of the filter
After the filter is created, it’s ready to use the newly created filter when assigning policies or apps. For example when deploying a new device configuration profile.
- Open the Device Configuration assignments settings
- Click Edit filter

Now the created filter is available. With the following options:
- Do not apply a filter
- Include filtered devices in assignment
- Exclude filtered devices in assignments
For including the filtered devices in the assignment. Select the option: Include filtered devices in assignment and select the created filter.
Now the filter is showed in the assignment overview. For saving the config; Review+save the settings.

Sources
For more information about using filters in Microsoft Intune. The following Microsoft sources:
Useful video from Scott Duffey (PM Microsoft)
Use filters when assigning your apps, policies, and profiles in Microsoft Endpoint Manager
Device properties, operators, and rule editing when creating filters in Microsoft Endpoint Manager
List of platforms, policies, and app types supported by filters in Microsoft Endpoint Manager
Filter reports and troubleshooting in Microsoft Endpoint Manager
Use Microsoft Endpoint Manager filters to target apps and policies to specific devices



