Working from home became the new normal in most of the work environments. With the increase of working from home also the security impact changed. During security incidents, most of the collaboration will be done with chat, email, or video, there is no option to walk into the next office to collaborate on security incidents. Microsoft released a new function to integrate Azure Sentinel incident handling with Microsoft Teams. With the new function, it is possible to create a virtual collaboration room. The collaboration room helps to ensure that all stakeholders, inside and outside the SOC are working as a team during the incident. From the Microsoft Teams interface you can use the default functions from Teams; OneNote, File explorer, and Collaboration.
Azure Sentinel collaborate with Microsoft Teams
Azure Sentinel’s Microsoft Teams collaboration allows security teams to seamlessly work together on recent security incidents. With the new feature, Azure Sentinel gives organizations the option to respond to potential cyberattacks from a virtual Teams room with all the stakeholders.
With the new integration Teams integration couple of new functions are available:
- Incident specific Microsoft Teams team
- Favorite groups
- Automatically added tabs for Post, Incident information and files.
- Automatic archiving
In this blog the usage of the new feature inside Azure Sentinel.
Note: Integration with Microsoft Teams is currently in Public Preview
Azure Sentinel Teams integration
For creating a new team some steps are required. Following the following steps for creating the new team:
- Go to the Azure Sentinel instance
- Open Threat Management -> Incidents (1)
- Open recent incident (2)

- From the incident page, open Actions -> Create Team (3)

From the Create team blade, some more details can be filled in. Based on the incident ID and Incident name a default name will be filled in. If needed it is possible to change the Team name for the specific incident.
Default naming-convention: Incident 211: Suspicious behavior by Microsoft Word was observed
Now add the group based on the AzureAD for the collaboration. For example the attached group: Security Analist T2 Group. This group contains all the members part of the T2 security analyst group. Note: It is always possible to select more groups if needed.
If you regularly work with the same teams, you can select the group as your favorite with the start icon.
Now press the button: Create Team.

After creating the Teams channel the direct link to the specific Teams can be found from the incident page or from the action screen.
For getting the incident link directly from the incident details page open the direct link from the Incident Team section.

Result: Incident Teams created from the Sentinel interface are available inside the Microsoft Teams environment.
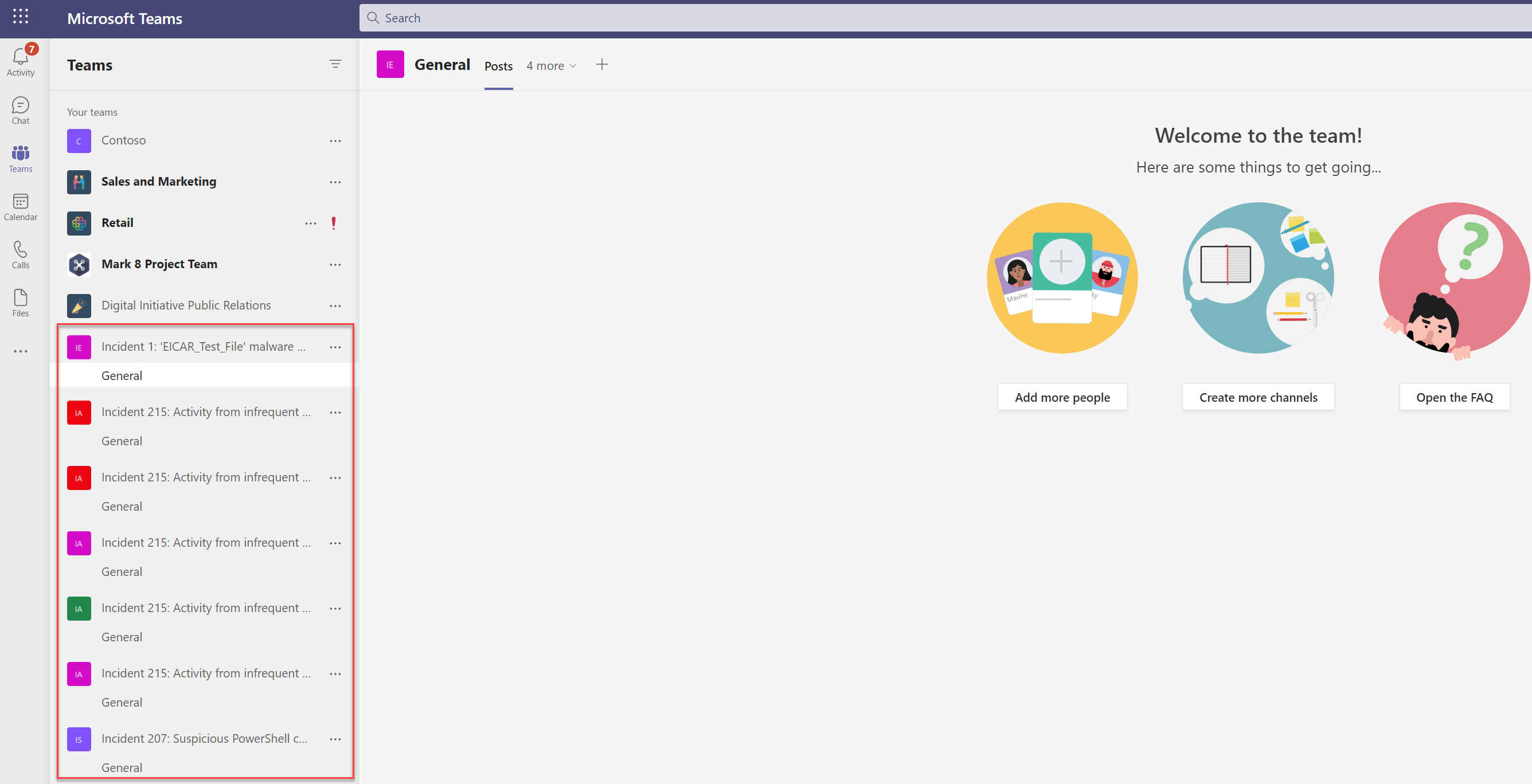
Teams channel
From the Teams view a new channel is created with the filled-in name. The access is linked to the Azure AD group attached from the Teams creation. The Teams channels are filled in with some default information:
- Incident page: Shows the incident details page from Azure Sentinel
- Files: Place to share files and information
- Teams post: Share Teams post/ messages
- Wiki: Create wiki with information incident-related information
From the Teams channel it is possible to start the conversation about the Sentinel investigation. The incident data is always up to date available from the Teams environment.
Incident page

Closed incident
When the incident is closed the created team for collaboration will be automatically archived. If the incident is ever re-opened, that team is also re-opened so that you can continue with the investigation and access all the available data.

Currently, the new feature is in public preview for most of the tenants. With the new feature, it is easier to integrate collaboration from Sentinel with Microsoft Teams for collaboration during incidents.
Sources
Microsoft: https://techcommunity.microsoft.com/t5/azure-sentinel/what-s-new-incident-team-collaborate-in-microsoft-teams/ba-p/2344376