Microsoft Defender for Office 365 is one of the three types of Advanced Threat Protection that Microsoft offers. With Microsoft Defender for Office 365 it is possible to secure the organization with advanced security features that keep you protection cybersecurity threats.
At the moment e-mail is one of the most pervasive and powerful forms of communication in a working environment. E-mail is still widely used worldwide for business and communication with colleagues and customers. For malware and attacks a good first start point. Due to the growing number of need for online communication, email remains a top security concern or for some a weakness in 2020. When it comes to email security, classic antivirus software will never block advanced social attacks.
Today more and more versions of email risks are developing. For example; Spear-phishing, spoofing, phishing, spam, viruses, ransomware, insider threats. Much more than just one spam mail. Time to secure the environment.
In this blog post, I want to show how you can use Microsoft Defender for Office 365 and the usage of the Configuration Analyzer. (release September/ October 2020)
Note; The features described in this topic are in Preview
What is Microsoft Defender for Office 365
Office 365 Advanced Threat Protection is the old based naming convention. Microsoft Defender for Office 365 is the new name of the product.
The Microsoft Defender products are renamed to a new branding; Editorial note; The post is based on the new Microsoft 365 naming convention.
- Microsoft 365 Defender (previously Microsoft Threat Protection).
- Microsoft Defender for Endpoint (previously Microsoft Defender Advanced Threat Protection).
- Microsoft Defender for Office 365 (previously Office 365 Advanced Threat Protection).
- Microsoft Defender for Identity (previously Azure Advanced Threat Protection).
Microsoft Defender for Office 365 is a cloud-based email filtering service that can help protect organizations from unknown malware and viruses. It can protect organizations with features like zero-day protection, unsafe attachments, and malicious links.
A view of threat protection:

What are the parts?
Prevention: Filtering stack including business email compromise, credential phishing, ransomware, and advanced malware.
Detection: AI-based detection of malicious and suspicious content and correlates attack patterns to identity campaigns designed to evade protection
Investigation and hunting: Powerful experiences help identify, prioritize, and investigate threats, with advanced hunting capabilities to track attacks across Office 365.
Response and remediation: Extensive incident response and automation capabilities amplify your security team’s effectiveness and efficiency.
Awareness and training: Simulation and training capabilities along with integrated experiences within client applications build user awareness.
Secure posture: Recommended templates and configuration insights help customers get and stay secure.
Product and license:
Microsoft Defender for Office 365 comes in two different Plan types.
Plan1:
- Safe Attachments
- Safe Links
- ATP for SharePoint, OneDrive, and Microsoft Teams
- ATP anti-phishing protection
- Real-time detections
Plan2: All of the Plan 1 +
Microsoft Defender for Office365 Plan 2 is included in Office 365 E5, Office 365 A5, Microsoft 365 E5 Security, and Microsoft 365 E5. Plan 1 is included in Microsoft 365 Business Premium. The Safe Documents feature is only available for users with Microsoft 365 E5 or Microsoft 365 E5 Security.
Check your policies using Configuration Analyzer
Configuration Analyzer is a new tool to analyze the environment to find and fix security issues when the settings are below Standard protection and Strict protection profile settings from the preset security policies.
Configuration analyzer is based on the following types of policies:
- Exchange Online Protection (EOP) policies
- Office 365 Advanced Threat Protection (ATP) policies
- ATP anti-phishing policies
- Spoof settings
- Impersonation settings
- Advanced phishing thresholds
- Safe Link policies
- Safe Attachments policies
- ATP anti-phishing policies
The analysis is based on the Standard and Strict baseline. The settings values can you find on the Microsoft website
Start with the Analyzer
Before you use the Configuration Analyzer you need to install the Exchange Online Powershell command. For the use and the change of some security settings if needed the following roles are required:
- Organization Management or Security Administrator in the Security & Compliance Center
- Organization Management or Hygiëne Management in Exchange Online
Read-only access is possible with the Security Reader role in Security & Compliance Center or View-Only Organization Management in Exchange Online.
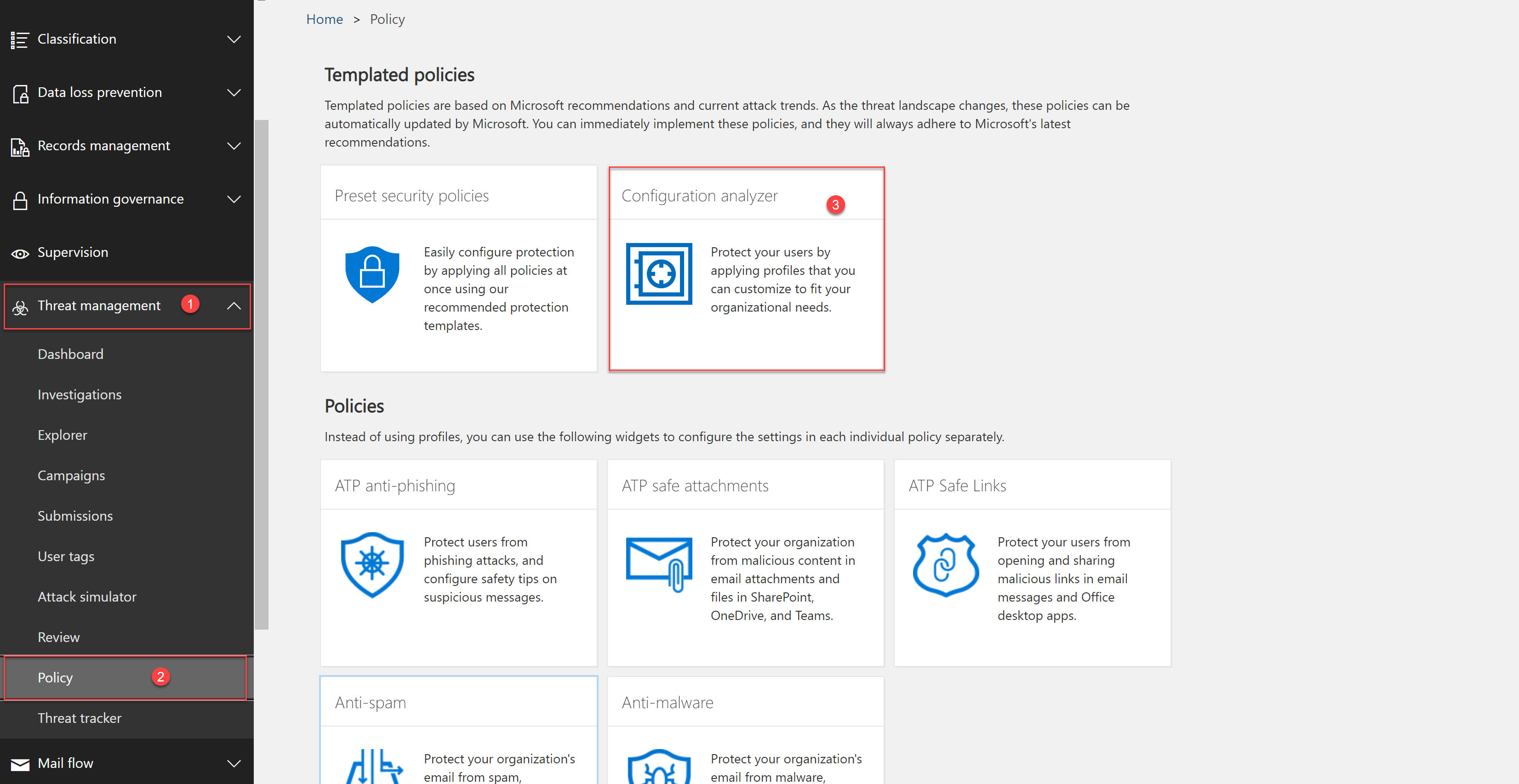
For the tooling go to the Security & Compliance Center:
- Go to Security & Compliance Center / URL; protection.office.com
- Click on Threat Management (1)
- Click on Policy (2)
- Click on Configuration analyzer (3)
Now you can see the Configuration analyzer dashboard with the tab Setting and recommendations. On the dashboard page, you can switch to Standard and Strict. For the switch;
Click on the text button; View Standard recommendations or View Strict recommendations.
Standard recommendations view:

Strict recommendations view:

In this view the settings are listed in different types of policies:
ATP Safe Attachments and ATP Safe Links are only available if your subscription included a license.

In the above view, you can see the different types of policies. Here you see the ATP Safe Attachments and ATP Safe Links settings configured based on the strict profile following the Microsoft Default. In the Anti-spam and Anti-phishing group, there a 7 and 12 recommendations. Let’s take a look:
Click now on Anti-spam for a collapsed view. If the comparison has no recommendations for improvement (green), expanding the policy reveals nothing. If there are any number of recommendations for improvement (amber or red), the settings that require attention are listed in the view with the following columns:
In the view:
- Setting name: Name of the settings. For example in the above screenshot the setting Spam detection action.
- Policy: Name of the policy where the settings are configured
- Applied to: The number of users that the affected policies are applied to
- Current configuration: This column listed the current value of the setting
- Last modified: The date that the policy was last modified
- Recommendations: The value of the setting from the Standard or Strict protection profile. For a direct change, click on adopt.

Based on the configuration the strict policy gives 7 recommendations for the anti-spam policy group with settings related to bulk email, quarantine retention, phishing email detection.
For the anti-phishing the following policies are detected:

When the policy is configured following the strict or standard recommendations the settings showed a green button.

Adopt the recommendations
Adopting policies is easy from the view. For this; Go to the Policy group, select the setting, and click on Adopt.
Info; the settings are configured from a Microsoft-based recommendation profile. Check always for possible conflicts and issues. See the tooling as an extra check and help-tool to possibly detect configuration issues.

Now click on confirm to change the current setting for bulk e-mail threshold from 7 to 4.

The status changed to green, with the info text; Recommendations successfully

Sources:
Microsoft; Office 365 Advanced Threat Protection service description
Microsoft; Microsoft Defender for Office 365 informational page




