Microsoft Sentinel is in the last months improved with a huge amount of new interesting features. One of the announced features is the content hub. In this blog the usage of the content hub and usage of the Teams / Training Lab content.
What is Microsoft Sentinel Content hub?
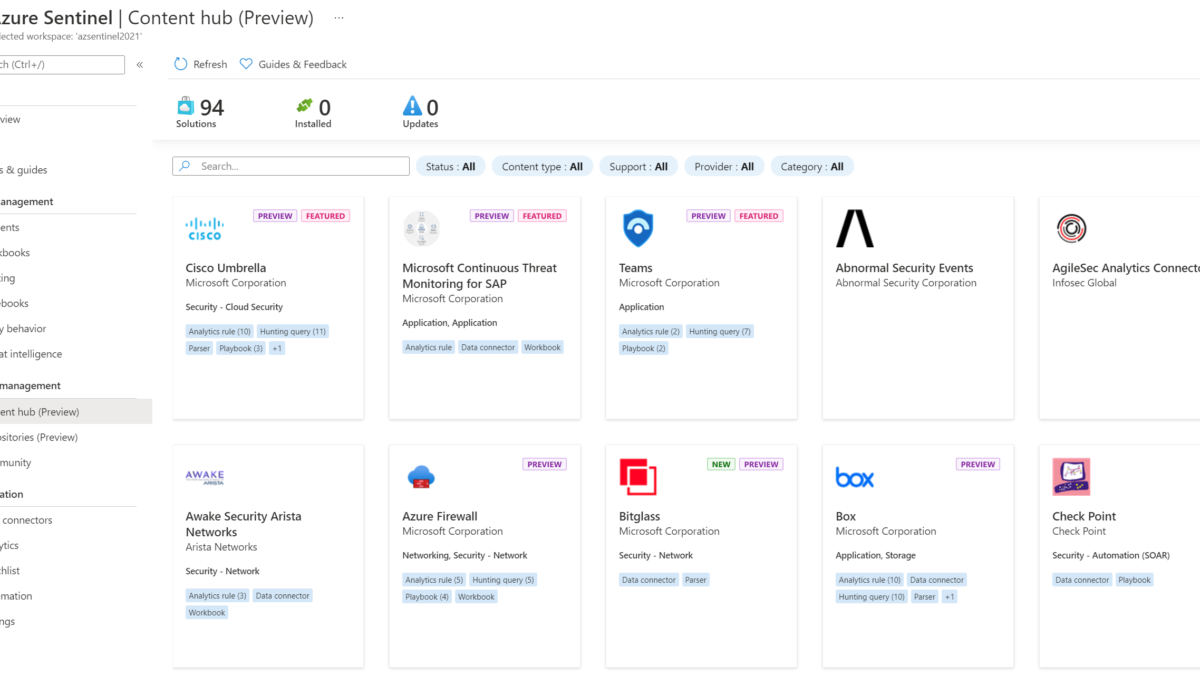
Microsoft Sentinel Content hub is currently in public preview and one of the latest features. With Content hub out-of-the-box content can easily be enabled and deployed. The new Content hub replaces the older solution gallery.
Microsoft Sentinel solutions are packages of pre-built content containing data connectors, workbooks, analytics rules, playbooks, or API integrations. At the time of writing (18-11-2021) 94 solutions are available. Part of the solutions:
- 41 Analytics rules
- 63 Data connectors
- 18 Hunting query
- 49 Parsers
- 16 Playbooks
- 42 pre-build Workbooks

Each pre-built package contains a set of content types. When clicking on the solution more details are visible. Each page contains the description, content type, category, and pricing details.
Content-type contains the types of content which will be installed. For example the solution Teams; which includes 2 analytics rules, 7 hunting queries, and 2 Playbooks.

Install Solution Package – Microsoft Teams
For using the new solution packages follow the below steps: (Example Microsoft Teams). The next chapter contains the Training Lab instructions.
- Go to Microsoft Sentinel
- Open Content Hub (preview)
- Open one of the available solutions
- Click Install
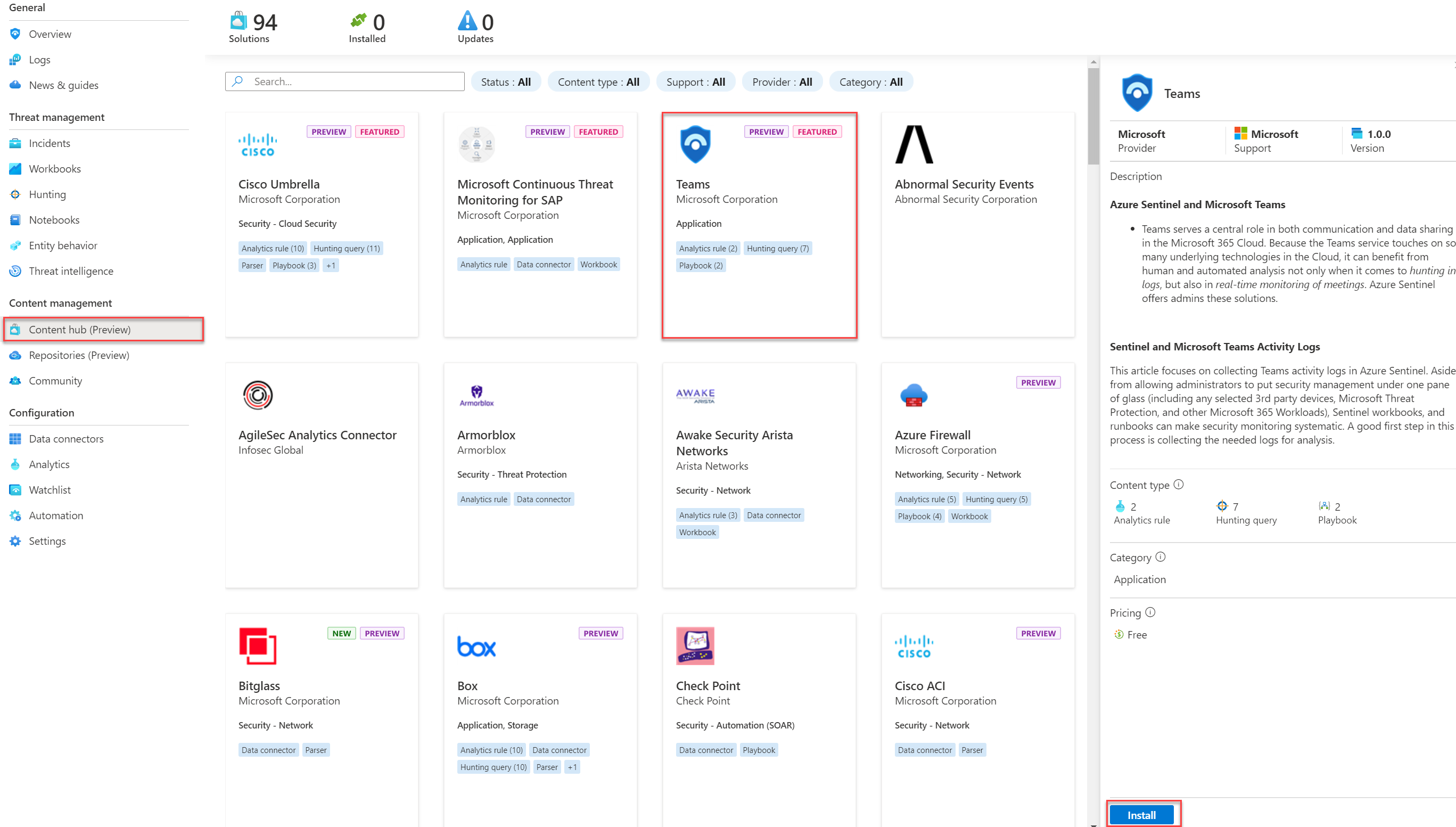
For completing the installation click on Create. The solution page contains general information, usage information + support, and community reviews.

Select the correct subscription, resource group, and Log Analytics workspace. Analytics, Huning Queries, Playbooks show which items will be created. If needed additional properties are visible to be configured.

With the result: Pre-created Analytics rules, hunting rules, API connections, and Logic apps.

Next part; The Training Lab content for getting hands-on Sentinel experience.
Install Solution Package – Training Lab content
The new Microsoft Sentinel Training lab solution allows users to have a full Microsoft Sentinel hands-on experience without deploying additional resources or generating any data from the typical data sources. All data is part of the Training lab solution.
What is including
The Training Lab solution package generates samples data directly into the Microsoft Sentinel workspace which will generate incidents.
This solution ingests pre-recorded data into your Microsoft Sentinel workspace and enables several artifacts for simulating scenarios. The ingested data size is around 20MBs so no high cost is related.
During the installation the pre-created data will publish in the following custom log tables:
- SecurityEvent_CL
- SigninLogs_CL
- OfficeActivity_CL
- AzureActivity_CL
Solutions created currently the following content:
- 2 Parsers
- 1 Workbook
- 3 Analytics rules
- 2 Hunting Queries
- 1 Playbook
Prerequisites
Before using the training lab content it is needed to use an existing Microsoft Sentinel workspace – or create a new workspace before deploying the solutions.
Install solution
For deploying the Training Lab go to Microsoft Sentinel and follow the steps described previously for the Teams solution. Search in the Content Hub for “Training Lab”

- Open the training lab solution and click Install
- Now click on Create and follow the configuration tabs.

Basics
Configure the correct Microsoft Sentinel Subscription, Resource Group, and Workspace during the setup. The selected subscription will be used to deploy all pre-defined content like data connectors, workbooks, analytics rules, and automation.

Workbooks
Part workbooks contain the configuration of the created workbook. By default, the solutions use the name Investigation Insights for the created workbook.

Analytics
The following Analytics rules will be created. These analytic rules will be deployed in a disabled mode in the analytics rules gallery of your Microsoft Sentinel workspace.
- Solorigate Network Beacon
- Sign-ins from IPs that attempt sign-ins to disabled accounts
- Malicious Inbox Rule
Hunting Queries
The following Hunting Queries rules will be created.
- Solorigate Inventory check
- Adding credentials to legitimate OAuth Applications
Watchlist
Pre-build watchlist with the name: HighRiskApps will be created. This watchlist will monitor the AAD application with the permissions and risk level.
Playbooks
The playbook with the name: Get-GeoFromIpAndTagIncident will be created. This playbook will take the IP address entities from the Incident table and query a Geo-IP API to geo-locate the IP Address. It will write the City and Country to a tag on the Incident. Playbook will be deployed directly in the previously selected Resource Group.
Review + create
After reviewing the configuration the solution will be installed by clicking on the button create.

The deployment takes around 10-15 minutes. During the creation, a PowerShell script uses the Log Analytics Data Collector API for ingested the telemetry stored in CSV format (Github). The API ingests the CSV telemetry data directly into the Sentinel custom tables.
Result Solution Package – Training Lab content
After installing the solution the pre-recorded data is directly visible in the following custom log tables:
- SecurityEvent_CL
- SigninLogs_CL
- OfficeActivity_CL
- AzureActivity_CL

Pre-created incidents:

Pre-created Watchlist with the name: HighRiskApps

Pre-created Workbook with the name: Investigation insights

Training Lab
After importing the training lab solution – the Microsoft Sentinel instance is ready for learning Microsoft Sentinel based on the imported data and available workbooks, playbooks, parsers e.d . Part of the solution is a training guide that provides instructions on how to navigate and use the features. View the Microsoft Sentinel training Lab which contains 8 modules
Sources
Microsoft: Learning with the Microsoft Sentinel Training Lab
Microsoft: Microsoft Sentinel Training Lab content
Microsoft: Imported Telemtry data