Microsoft Defender for Endpoint is available for multiple platforms including Windows, macOS, and Linux. For mobile platforms Defender for Endpoint is available for iOS and Android. Multiple methods are available for deploying Defender for Endpoint on iOS devices.
This blog focuses on Defender for Endpoint on iOS devices using the MEM/ Intune mode for supervised/ unsupervised devices. Another blog will be written focussed on unmanaged devices via Mobile Application Management (MAM) policies.
| Blog information: Blog published: February 18, 2023 Blog latest updated: February 18, 2023 |
Introduction Defender for Endpoint on iOS
Defender for Endpoint on iOS enables protection against phishing/ jailbreak detections and unsafe network connections. All signals and data are part of the centralized Defender 365 portal. There are various methods and options available for deploying Defender for Endpoint on iOS; for example in supervised and unsupervised mode. More detailed information is included in this blog; including the options/ best practices and recommended way of deployment.
For using Defender for Endpoint on iOS validate the following prerequisites:
- Microsoft Defender for Endpoint license assigned
- Intune license available
- iOS device running iOS 14.0
- Device registered with Azure Active Directory via Authenticator app or enrolled with Intune Company Portal app
More information: Prerequisites Microsoft Defender for iOS
Available deployment options
Deployment is possible via various methods. In general, deployment is possible with the use of Microsoft Intune for the following situation:
- Deploy Defender for Endpoint on enrolled devices via MEM/ Intune (supervised/unsupervised mode)
- Deploy Defender for Endpoint using app protection policy (MAM)
| Recommended is to use the supervised mode for corporate-managed devices. Supervised mode enables more features in Intune (Locate device, lost mode) |
Deployment using Intune
Enable Intune connector
Deploying using Intune is available for both supervised and unsupervised devices. First, we need to ensure the Microsoft Intune connector is enabled in the Microsoft 365 Defender portal.
Go to Settings -> Endpoints -> Advanced features and enable the feature Microsoft Intune connection

Now we need to allow iOS devices in the Microsoft Endpoint Manager admin center for sending compliance information, optional enable the App protection policy evaluation for iOS devices. To enable the feature for iOS, follow the following steps:
- Open Microsoft Endpoint Manager admin center
- Navigate to Endpoint Security -> Microsoft Defender for Endpoint
- Now configure the: Connect iOS devices to Microsoft Defender for Endpoint to On

Prepare app deployment
Defender for Endpoint is part of the Apple App Store. First, we need to add the app to the Endpoint manager admin center.
- Go to Apps-> iOS/ iPadOS -> Add -> iOS store app and click Select.
- Search for the app with the name; Microsoft Defender

- Select iOS 14.0 as the minimum operating system. Defender for Endpoint requires iOS 14.0 or higher. For lower versions, the app will be not deployed/ installed when configured as a minimal operating system.

- Deploy the app to one of the user group(s) as required app. It is recommended to test first on a couple of test users before deploying the app to larger groups.
Supervised mode via Intune
The supervised mode gives greater control over iOS devices owned by a company and enables additional device configurations and features. By default; all iOS devices are not supervised. To determine if a device is supervised, there is the following information visible on the main local screen: On the device’s lock screen, it will say This iPhone is managed by “Company Name”. See: Turn on iOS/ iPadOS supervised mode for more options using enrollment profiles in DEP.
For supervised devices, there is the option for configuring additional management capabilities for a more seamless management experience. The supervised mode can be configured for managed devices and should be targeted to all managed iOS devices.
Benefit: When using the supervised mode the Defender for Endpoint VPN profile will not be installed on the device. The web protection is provided by the imported control filter profile. The VPN-less solution is only available for devices in the supervised management state.
App configuration profile
For enabling the supervised mode we need to configure a new App configuration policy and configure the issupervised configuration key.
- Go to Apps > App configuration policies > Add. Select Managed devices
- Add a custom name and selected the platform iOS/ iPadOS. As app select the Microsoft Defender Endpoint application.
Use the configuration designer for configuring the issupervised configuration key. Add the following information in the configuration designer:
| Configuration key | Value type | String |
| issupervised | string | {{issupervised}} |
Device configuration profile (zero-touch) for devices
Devices enabled in the supervised mode are supported with the custom .mobilconfig profile. This profile configured the web protection capabilities seamlessly without setting up the local configuration or manual actions the local user performs.

Download the .mobileconfig configuration profile here: ControlFilterZeroTouch
| Important: For supervised devices, there is no local/self-looping VPN required. The control filter contains the local web filtering policy. |
Unsupervised mode via Intune
Unsupervised is the default for iOS devices (Supervised is only enabled when configured, default out-of-the-box devices are unsupervised). There are configurations available for the unsupervised devices to zero-touch onboard Microsoft Defender for Endpoint. Zero-touch is available for devices that are registered with a user account.
Important: The Defender for Endpoint VPN profile is not a regular VPN connection and is only based on local/self-looping. There is no outgoing traffic as part of the VPN profile. When using the VPN profile it is needed to add the VPN configuration. Recommended is to use the zero-touch silent onboarding.
Zero-touch for unsupervised devices
| Important: The VPN profile should be deployed to unsupervised devices. For supervised devices it is not needed to configure the VPN profile. |
For unsupervised devices, it is possible to configure Defender for Endpoint silent using zero-touch configuration – where the user is only notified of the installation and enablement of the web protection feature. For zero-touch it is required to configure a configuration profile in Intune:
First, we need to configure the custom VPN profile as a configuration profile in Intune. With this zero-touch (silent) onboarding method the user received the notification and Defender for Endpoint is automatically installed without the need for configuring the device on the iOS phone itself.
- Open Endpoint Manager admin center
- Navigate to Devices -> Configuration Profiles -> Create profile
- Select the platform iOS/ iPadOS and the profile type VPN
- Fill in the custom configuration profile name
- Configure Custom VPN

Now it is time to configure the Base VPN and Automatic VPN configuration. For configuring the correct profile use the below settings:
- Base VPN settings
- Connection Name = Microsoft Defender for Endpoint
- VPN server address = 127.0.0.1
- Auth method = “Username and password”
- Split Tunneling = Disable
- VPN identifier = com.microsoft.scmx
- Key-Value: SilentOnboard with value to True
- Key-Value: SingleSignOn with value to True
With the result:

- Automatic VPN settings:
- Type of Automatic VPN = On-demand VPN
- On-demand rules: I want to restrict Connect VPN for all domains
To require that the VPN can’t be disabled it is possible to configure the setting: block users from disabling automatic VPN with the value Yes. By default, the VPN deployment is enabled again within some seconds after the disablement.
With the result:

When using the zero-touch configuration profile all settings will be enforced automatically without any user impact. The iOS devices will be automatically onboarded and the devices are visible in the Defender for Endpoint portal. The user receives a notification when the installation is completed.
For non-supervised devices, it is required to configure the local/ self-looping VPN for enabling web protection capabilities. Via App configuration policies it is possible to disable the web protection/ network protection feature for devices.
More information: Disable Web Protection
Configure Network Protection
Network Protection is by default disabled for all iOS endpoints. Using App configuration policies it is possible to enable this feature.
For Intune-enrolled devices, it is possible to configure Network Protection using app configuration policies.
- Open Endpoint Manager admin center
- Navigate to Apps > App configuration policies > Add > Managed devices
- Select the platform iOS/ iPadOS
- Select the target app; Microsoft Defender for Endpoint
Use the configuration designer for configuring the issupervised configuration key. Add the following information in the configuration designer for enabling Network protection.
| Configuration key | Value type | String |
| DefenderNetworkProtectionEnable | string | true |

Additional configurations are available for additional fine-tuning around the policies:
- DefenderOpenNetworkDetection
- DefenderEndUserTrustFlowEnable
- DefenderNetworkProtectionAutoRemediation
- DefenderNetworkProtectionPrivacy
More information: Configure Network Protection
App inventory visible in Defender for Endpoint?
Common question; all iOS phones are enrolled, all there is no vulnerability assessment data available for all apps.
Currently, vulnerability assessments of apps are available for enrolled (MDM) devices. By default, this feature is not enabled for supervised/ unsupervised devices.
Configuration is possible in Microsoft Endpoint Manager admin center. After the configuration processing of all data takes a couple of hours max to 24 hours to complete.
Supervised devices
Go to Endpoint Security > Microsoft Defender for Endpoint and enable the feature Enable App sync for iOS/iPadOS devices

Unsupervised devices
For unsupervised devices more configuration is required. Enable the following features; Enable App Sync (sending application inventory) for iOS/iPadOS devices and optional Send full application inventory data on personally owned iOS/iPadOS devices
| With the setting; Send full application inventory data on personally owned iOS/iPadOS devices unmanaged apps can be discovered (apps not deployed via Intune) On corporate devices, any app whether or not it is a managed app will always be included in the list of applications from Intune. This configuration relays on the available privacy policy for unmanaged device data collection and it depends on the organization’s requirements. |
Compliance policy
The device compliance policy can be used when Intune is configured. When the iOS device is on a specific risk level it is possible to mark the device as a non-compliant device and take additional actions using Conditional Access.
The following setting is required for the compliance policy evaluation: Connect iOS/iPadOS devices version 13.0 and above to Microsoft Defender for Endpoint

When configured the device risk score can be used in the calculation for the compliance policy. For example; require the device to be at or under the medium machine risk score:

Result
When all policies and apps are correctly deployed the machine is visible in Defender for Endpoint. Always confirm the onboarding state – make sure it is onboarded with the status; Onboarded and not Can be onboarded. After the onboarding confirm the information and available data.
Alert
Use the SmartScreen demo website for testing the initial web protection feature. URL: smartscreentestratings2.net
SmartScreen generates the following alert in MDE; Device tried to access a phishing site

Device
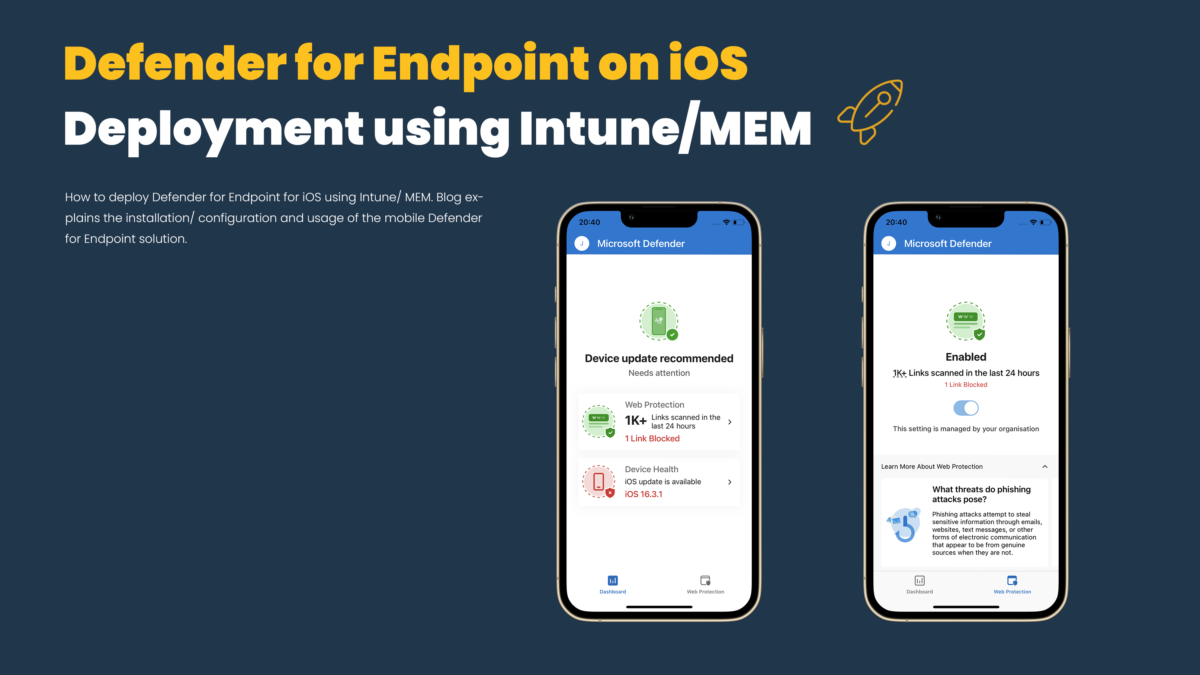
Locally on the iPhone, the following is visible:
- Main screen of Defender for Endpoint for iOS
- Custom-added (indicator) website blocked by Defender for Endpoint for iOS
- Settings overview (VPN configuration)



Defender for Endpoint portal
Portal view:

Timeline view:

Vulnerability view:

Sources
Microsoft: Microsoft Defender for Endpoint on iOS
Microsoft: Microsoft Defender for Endpoint – Mobile Threat Defense




Hey Jeff,
thanks for the great content regarding this topic.
One question regarding this section “Device configuration profile (zero-touch) for devices”.
That profile needs to be deployed to the users’ group or iOS devices?
I am asking as we are distinguishing between corporate and personal devices.
I guess if that would be users deployment I can use filters that would filter on corporate devices?
Many thank in advance for the reply.
Hi Jeff,
Excellent article!
Is there a method to apply update policies on unsupervised iphones?
Thanks for the taken effort and have a nice day!