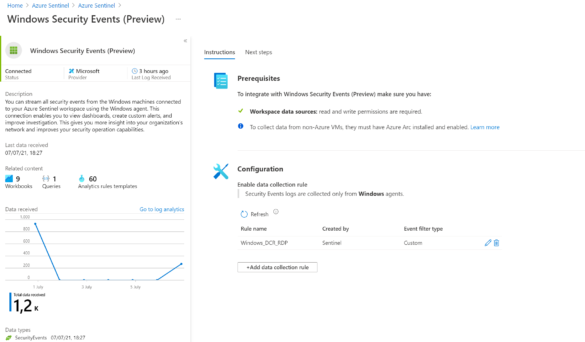
Using the Azure Sentinel Windows Security Events Connector for getting custom events
Microsoft announced on 14th June 2021 a new version of the Windows Security Events data connector. The new feature reached currently the public preview release. In comparison with the current public Security Events connector some new improvements are added for…
PrintNightmare – Use Microsoft Defender/ Sentinel toolings to get insights
Technical details and a proof-of-concept (PoC) exploit have been accidentally leaked for a currently unpatched vulnerability in Windows that makes remote code execution possible. The issue affects Windows Print Spooler. The researchers named it PrintNightmare. Currently, the latest June 2021 security…
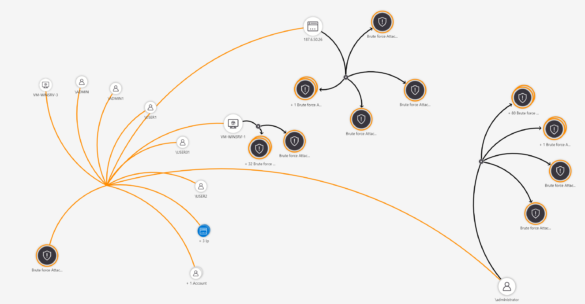
Monitor RDP Brute Force Attack with Azure Sentinel & Azure Security Center
Since the last years, there is a large increase in cybercriminals attempting to run attacks by exploiting the login credentials. With the current work-from-home scenario, more attacks are visible against the RDP protocol. At the moment one of the most…
Review service principals with Azure AD Access Reviews and monitor with Azure Sentinel
A new feature in public preview is the Azure AD access review functionality. With the new AzureAD access reviews function it is possible to review service principals in the Azure environment. With the more growing trend of cloud services and…
Monitor Azure AD break-glass accounts with Microsoft Sentinel
Conditional Access configuration for AzureAD accounts is important. With Conditional Access you can protect easy accounts, block outdated protocols and create more security cases to protect corporate data. An important part of Conditional Access is the usage of break-glass accounts….
Export Microsoft 365 Defender security events with the streaming API
By default Microsoft Defender for Endpoint stores Endpoint events in Defender for Endpoint for the configured retention period; Max: 180 days. For longer data retention it is possible to export events to external sources, most typical; Azure Storage or Azure…
Enroll Android smartphones into Microsoft Defender for Endpoint for blocking FluBot
The Flubot-malware is currently active in the news. The malware with the name FluBot will be sent to mobile endpoints with a text message or WhatsApp message. When opening the link and installing the app the FluBot malware will be…
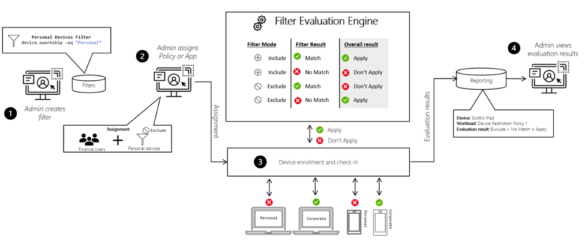
Endpoint Manager filters: Use filtering for assigning policies, profiles and apps to specific devices
Microsoft recently announced a new existing feature in Microsoft Endpoint Manager with the name: “filters”. With the new feature, it is easier to create a specific deployment and exclude specific device groups. For example excluding virtual desktop machines from the…
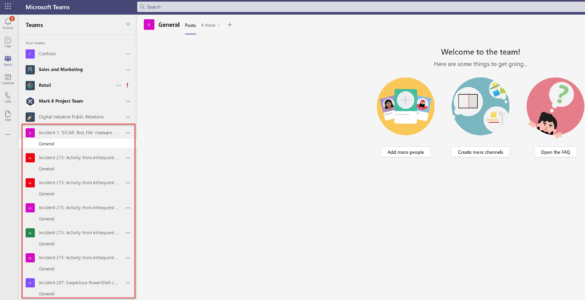
Integrate Azure Sentinel with Microsoft Teams for seamlessly collaboration
Working from home became the new normal in most of the work environments. With the increase of working from home also the security impact changed. During security incidents, most of the collaboration will be done with chat, email, or video,…
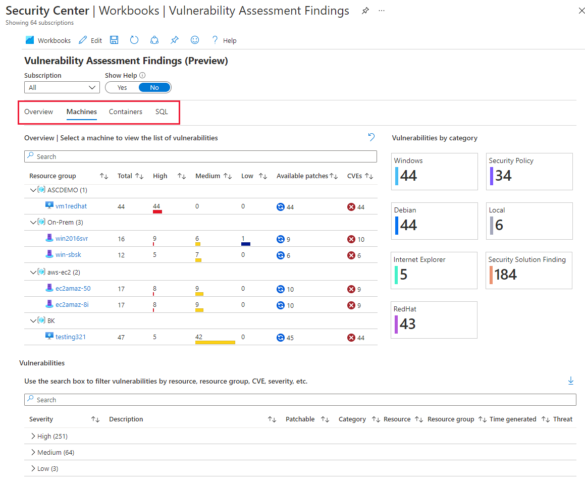
Use Azure Security Center workbooks for detailed information/ dashboards
Azure Security Center included integration with Azure Workbooks. With the new Workbooks feature is it possible to build custom reports. From Azure Security Center there is integration with Azure Workbooks. By default Azure Security Center included three new dashboards for…