Content updated: 8 December 2020. Changes or newer versions/ information can be released by Microsoft.
Microsoft Defender for Endpoint is now generally available for iOS devices. Microsoft Defender now works on multiple platforms; macOS, Linux, Android, and now iOS. With the Defender for Endpoint enrollment for iOS devices you will get multiple security features; like anti-phishing, custom indicators and blocking unsafe connections.
Microsoft Defender for Endpoint for iOS will offer protection against phishing and unsafe network connections from websites, emails, and apps. With this function it is possible to protect devices against phishing.
Introduction Microsoft Defender for Endpoint
Microsoft recently announced the public availability for Microsoft Defender for Endpoint for iOS. Previously known as Microsoft Defender ATP for iOS. All events and alerts around phishing and unsafe network connections will be available in Security Center. With compliance policy’s it is possible to use the device risk information to block devices and connection to company data. The main capability of MDE for iOS is at the moment web protection. Technical wise the web protection features use a self-looping VPN that does not take traffic outside of the device. With this feature it is possible to blocking access to unsafe websites coming from mails, browsers, iOS apps or SMS-messages.
Before the start – Licensing
Before you start with Defender for Endpoint on iOS devices. Confirm the licenses and add-on. For the Microsoft Defender feature, you need one of these subscriptions.
- Windows 10 Enterprise E5
- Windows 10 Education A5
- Microsoft 365 E5 (M365 E5) which includes Windows 10 Enterprise E5
- Microsoft 365 E5 Security
- Microsoft 365 A5 (M365 A5)
Prerequisites
Some pre-requisites are needed for a correct enrollment.
- Microsoft Defender for Endpoint license assigned to the end-user.
- Devices enrolled via Intune Company Portal app
- iOS 11 or above Note: For Intune Company Portal app minimal iOS 12 required
- Correctly enrolled with the Intune Company Portal app
Integration with Microsoft Endpoint Manager
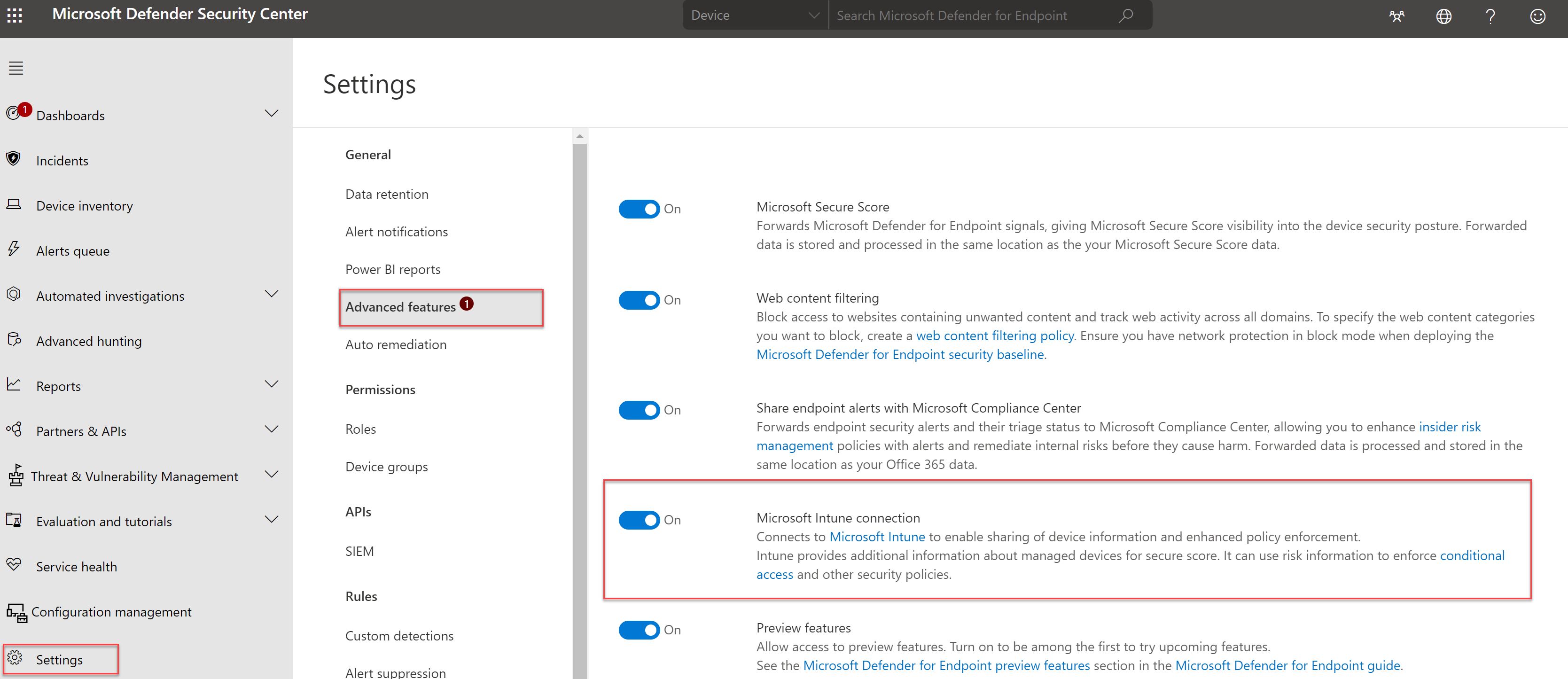
Defender for Endpoint makes it possible to integrate with Microsoft Endpoint Manager. With the integration, it is possible to share risk-level information. The connection with Microsoft Endpoint Manager can be enabled in the Microsoft Defender Security Center portal.
- Open Microsoft Defender Security Center
- Navigate to Settings -> Advanced features
- Configure the Microsoft Intune Connection.
Now we need to allow iOS devices in the Microsoft Endpoint Manager admin center. For iOS or Android it is possible to specify the integration.
To enable the feature for IOS, follow the following steps:
- Open Endpoint Manager admin center
- Navigate to Endpoint Security -> Microsoft Defender for ATP
- Now configure the: Connect iOS devices of version 8.0 and above to Microsoft Defender ATP to On
With this feature the compliance policy integrates with Microsoft Defender for Endpoint.

Deployment of the iOS app
Now it is time for the app deployment. In this specific case we using Endpoint Manager for the deployment. For the deployment of the Microsoft Defender ATP app go to Microsoft Endpoint Manager Center.
Note: Microsoft Intune is the only supported Mobile Device Management (MDM) solution for deploying Microsoft Defender for Endpoint for iOS. Currently only enrolled devices are supported for enforcing Defender for Endpoint for iOS related device compliance policies in Intune.
- Open Endpoint Manager admin center and navigate to the apps panel.
- Now click on Apps -> All Apps -> iOS/iPadOS
- Click Add and select the iOS Store app as App type

- Search the app in the App Store. Use the searchterm; Microsoft Defender ATP

- If needed add now more app information details. Description, publisher, notes, etc.
- Now assign the Microsoft Defender ATP application to a user or device group.
Integrate with compliance policy
If the iOS devices find a malicious connection it is possible to use the device risk to mark the device as non-compliant. With a compliance policy it is possible to restrict access to company apps and data. For this specific blog post an example.
- Go to Microsoft Endpoint Manager
- Navigate to Device -> Device Compliance Policies
In the Policy screen it is possible to create new compliances policies. For now we create a specific compliance policy for iOS/iPadOS.

In the compliance policy wizard you can specify multiple settings. For example; the minimum OS version. For Microsoft Defender for Endpoint it is interesting to use the Device risk score. With the policy it is possible to specify the machine risk score to be at or under the configured machine risk score.

To extend the compliance policy information for specific apps and data you can create a conditional access policy that required a compliant device.
Defender for Endpoint for iOS supports creating custom indicators only for IP addresses and URLs/domains. For the example to block www.nu.nl
- Open Defender for Endpoint portal
- Go to settings -> Rules and click on indicators
- Now open the tab -> URLs/Domains

- Add the website; for example www.nu.nl

The result
The end result is the deployment of the Defender ATP app and sharing for the compliance state to Microsoft Endpoint manager.

With the test of the web protection option, you can use the test website smartscreentestratings2.net
The user will receive the “malicious site blocked notification”. From the Security Center portal the event will be logged as “informational”
The result without Defender for Endpoint enabled:

The result with Defender for Endpoint enabled:


VPN configuration:

And the example website nu.nl blocked with a custom indicator:

Administrator view
From the administrator experience, you can find some alerts in the Microsoft Defender Security Center portal. The alerts detect a phishing site detection and showed outbound connection info.


Sources
Microsoft: https://docs.microsoft.com/en-us/windows/security/threat-protection/microsoft-defender-atp/microsoft-defender-atp-ios
Microsoft: https://techcommunity.microsoft.com/t5/microsoft-defender-for-endpoint/microsoft-defender-for-endpoint-on-ios-is-generally-available/ba-p/1962420




